Downloadables (Checklists, Cheat Sheets & Guides)
Featured Videos
Explore the Latest Trends in IT
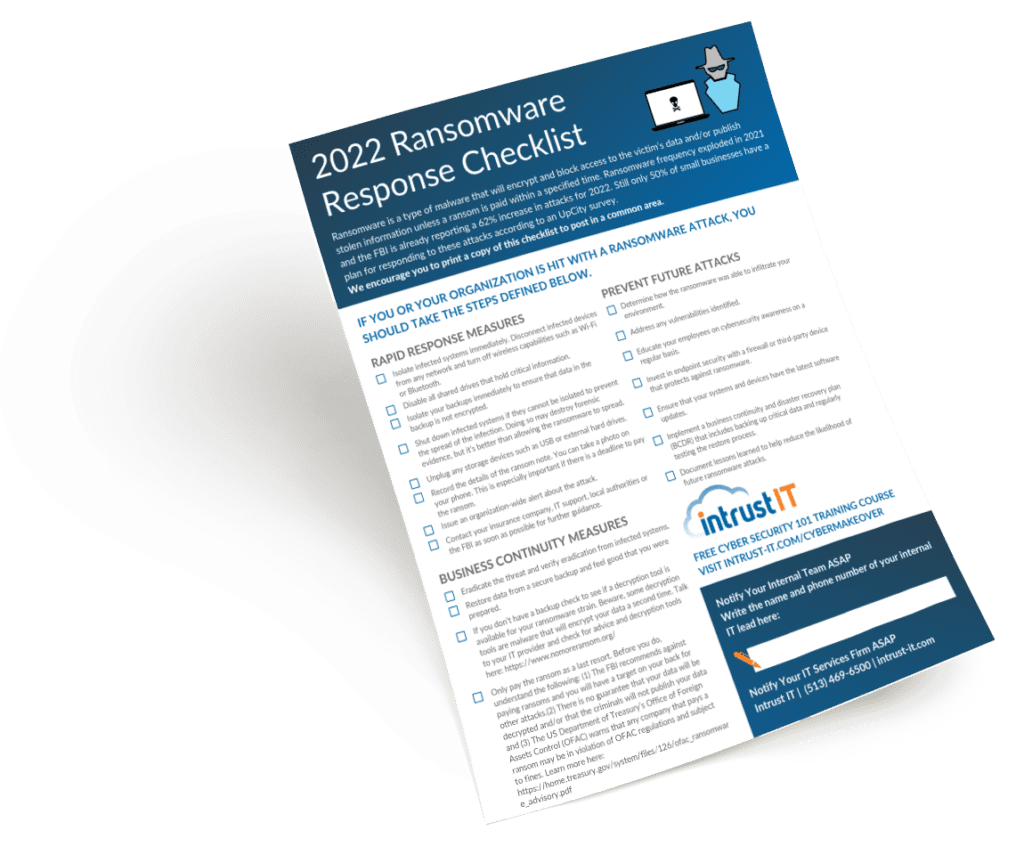
Download the Ransomware Response Checklist 2022
Would you know what to do if you fell victim to a ransomware attack? Download this free printable checklist. The...

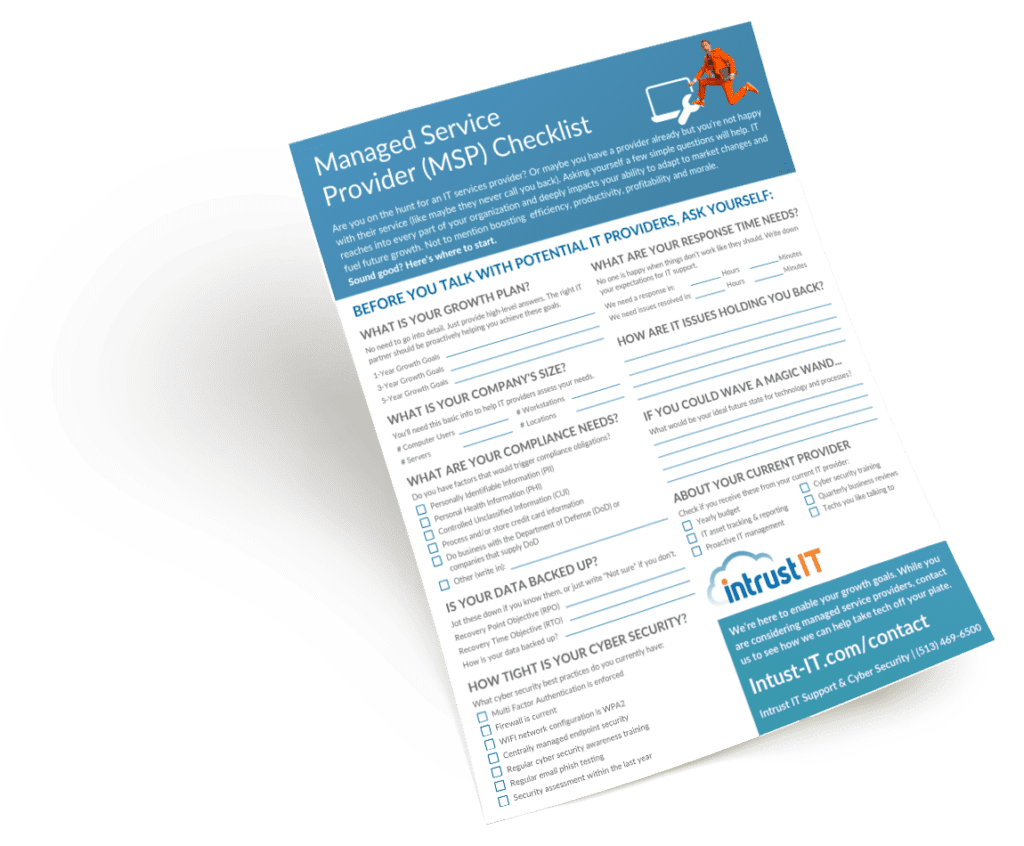
Choose Cincinnati IT Support for Business with our Managed IT Checklist
How to Choose IT Support for Business Finding a managed IT support company for your business can be a little...
How One Client Saved 28K with Microsoft Office 365 Auditing
We saved one client over $28,000 per year on Microsoft Office 365 licenses through our Office 365 auditing process. Here...

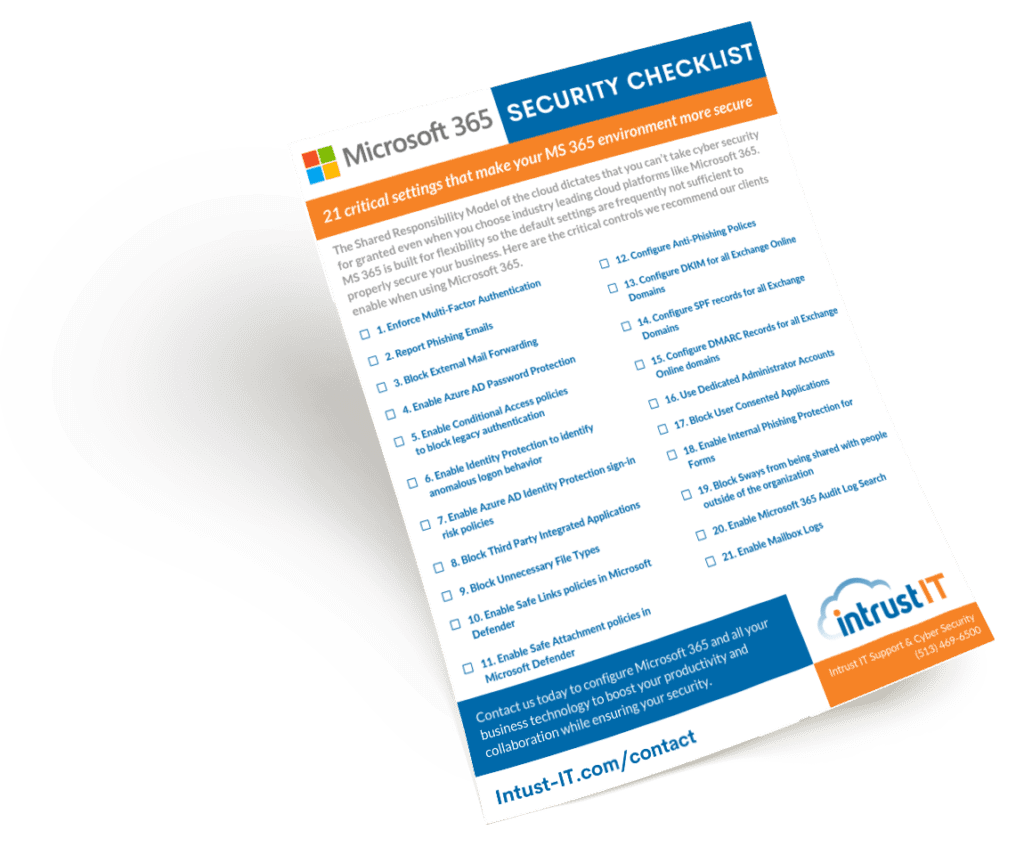
Managed Microsoft 365: 9 Benefits of Managed IT Services
If you are using or considering Microsoft 365 for your business? Consider this: Managed Microsoft 365 is even better. Managed...
Request a SCAP Compliant Vulnerability Assessment
Our advanced, non-invasive internal and external scans can identify security, performance and stability issues in your network. Get a preliminary scan followed by in-depth consultation with our technical and compliance specialists. After some time to consider the findings, we'll run another round of scans and consultations before providing the final report.