IT Outsourcing Service: Deciding Between Managed and Enterprise IT Services

IT Outsourcing Service: How to Decide on Support Levels
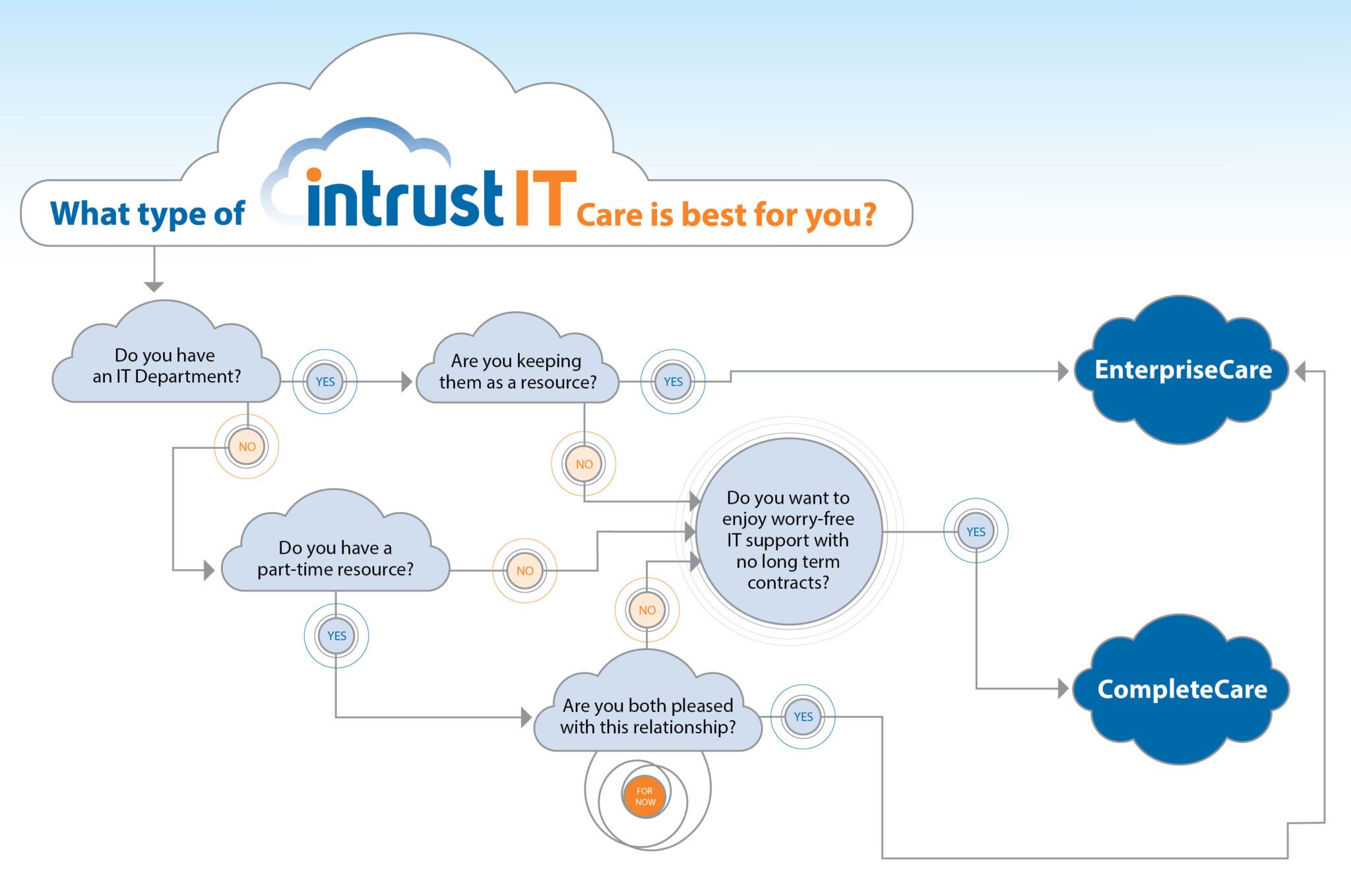
Considering an IT outsourcing service? One important consideration is the level of care you need. Are you looking for a complete IT outsourcing service or do you need enterprise IT services? We created this decision matrix below to help.
IT Outsourcing Service Decision Matrix
Understanding CompleteCare Managed IT Services
Our CompleteCare IT Managed Service offering is right for you if you are looking to completely outsource your worry. From security and monitoring to the smallest details with email and setup, we do it all. You don’t have to think about your IT, except maybe random thoughts about how smoothly it is working.
Learn about our CompleteCare IT Managed Service offerings for small businesses.
Understanding EnterpriseCare IT Services
Our EnterpriseCare IT support service offering is right for you if you have an IT department and you like them, but they are overwhelmed trying to keep up with the ever-evolving world of IT. Our team will help them when and wherever needed.
Learn about our EnterpriseCare IT Support Service offerings for small businesses.
Still Confused About Outsourced IT Services?
We created a comparison page with all the details of each package. Check out our IT service packages comparison page. Or book an appointment and we can call or visit your office. Or even message us on our Intrust IT Facebook page. Schedule an Appointment
Share this Blog

Is Your Name or Birthday a Part of Your Password?
If so, you’re a part of the 59 percent of people who don’t follow proper password hygiene. More than 70 percent of passwords are used for more than one system, meaning if cybercriminals crack one, they can access a lot more accounts.
Our free Enterprise Password Management Guide will give you the best password hygiene practices to help you secure your computer and your business.
Download the Guide
Explore the Latest Trends in IT

Microsoft 365 and Google Workspace: The Importance of Backing Up Your Cloud-Based Applications

AI Guiding Principles

Edge vs Chrome Security: Which Is the Best Browser for Your Business?




