Active Invitation to Bid Phishing Alert

Phishing Alert: We have observed an active phishing actor who has been compromising many companies in the Cincinnati area. After compromising a user’s email account, the attacker has been observed to look for sensitive information in the mailbox and then send out a mass email from the victim’s account with a link pointing to a phishing site hosted by the attacker used to steal additional users’ credentials.
Since January 20, 2022, prompting our phishing alert, we have seen many of our clients targeted by this threat actor, with the phishing emails coming from many different compromised companies in the Cincinnati area. In all the emails we have seen, the threat actor has been using very similar tactics and techniques to perform this attack.
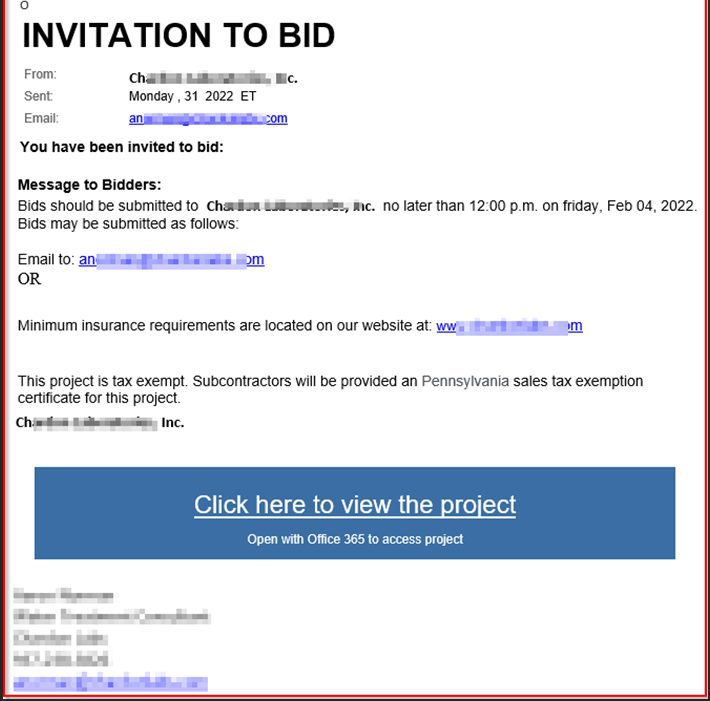
From what we have seen so far, the subject of the phishing emails starts with “Invitation to Bid – : ” and then includes the compromised company name in the subject. For example, if Company A was compromised, the subject would be “Invitation to Bid – : Company A”.
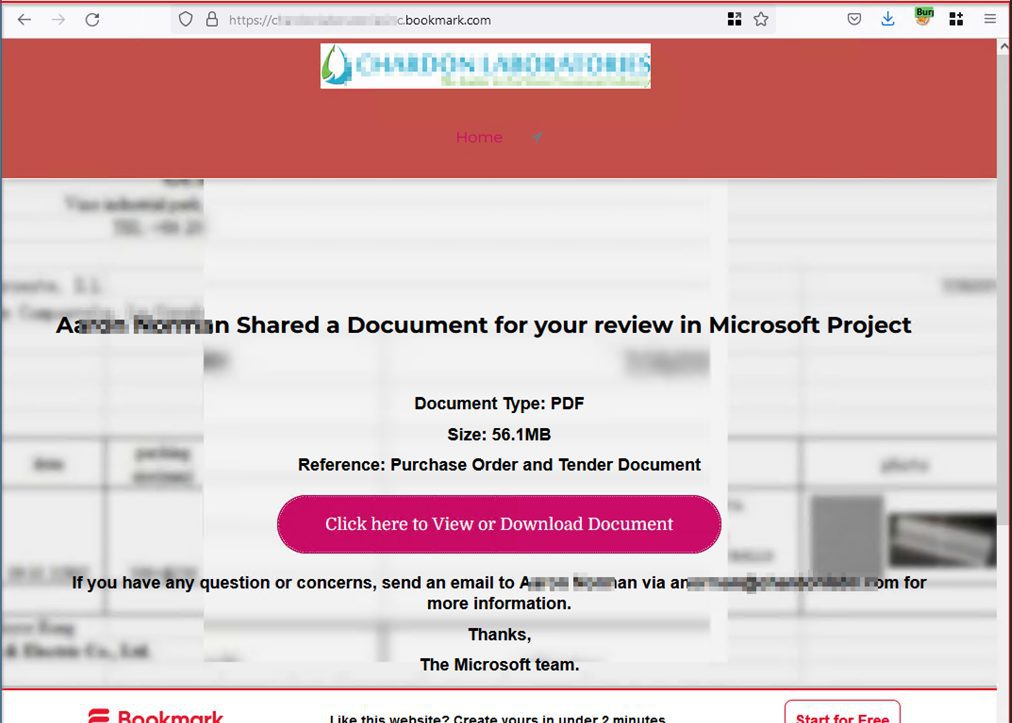
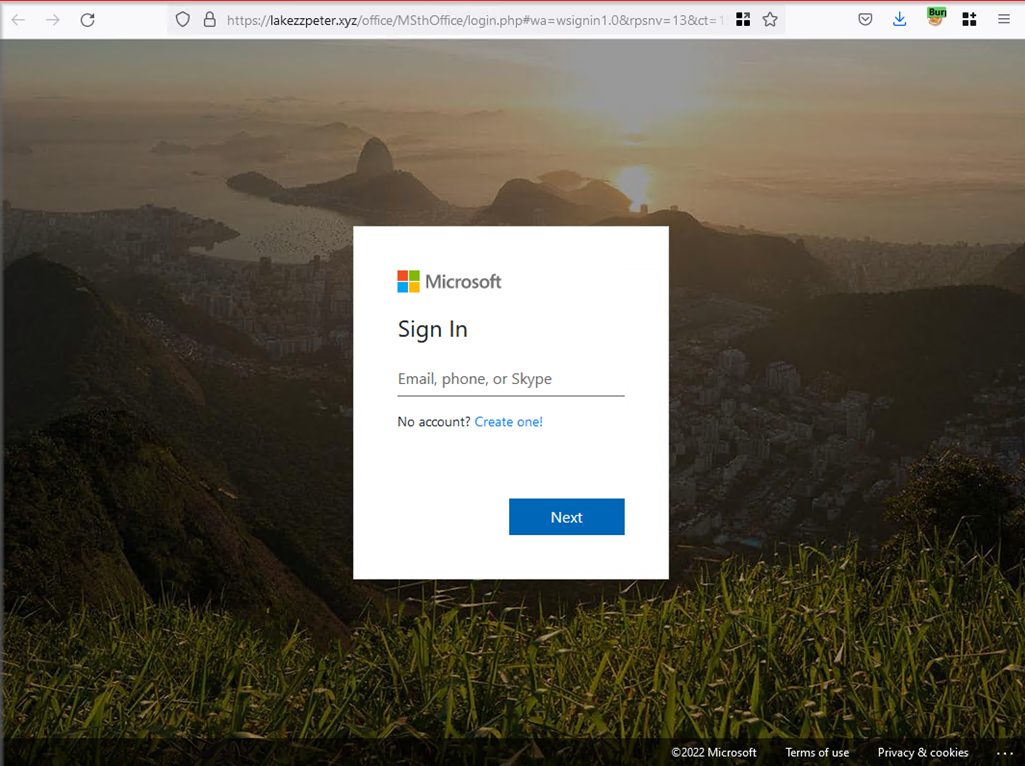
The phishing email itself has a link pointing to an initial landing webpage, which itself is not harmful, but it contains a link to another site hosting a fake Microsoft login page, which is used to steal users’ credentials. The initial location of the landing page is hosted on a platform that has legitimate use cases, making it difficult for security teams to block without potentially impacting legitimate business operations.
Phishing Alert: Example Email
Example Initial Phishing Webpage
Look-a-like Microsoft Webpage
Share this Blog

Is Your Name or Birthday a Part of Your Password?
If so, you’re a part of the 59 percent of people who don’t follow proper password hygiene. More than 70 percent of passwords are used for more than one system, meaning if cybercriminals crack one, they can access a lot more accounts.
Our free Enterprise Password Management Guide will give you the best password hygiene practices to help you secure your computer and your business.
Download the Guide
Explore the Latest Trends in IT

Microsoft 365 and Google Workspace: The Importance of Backing Up Your Cloud-Based Applications

AI Guiding Principles

Edge vs Chrome Security: Which Is the Best Browser for Your Business?




